Welcome to The B
IRT Project.
Our goal is to support incident responders by providing them
with effective tools that exceed their needs. As a 100% bootstrapped project, we are motivated by
our extensive experience in cybersecurity and a deep understanding of the challenges faced
in incident response. We recognize the need for quick and accurate responses in the face of
today's changing threats.
Download the Free Beta Today!
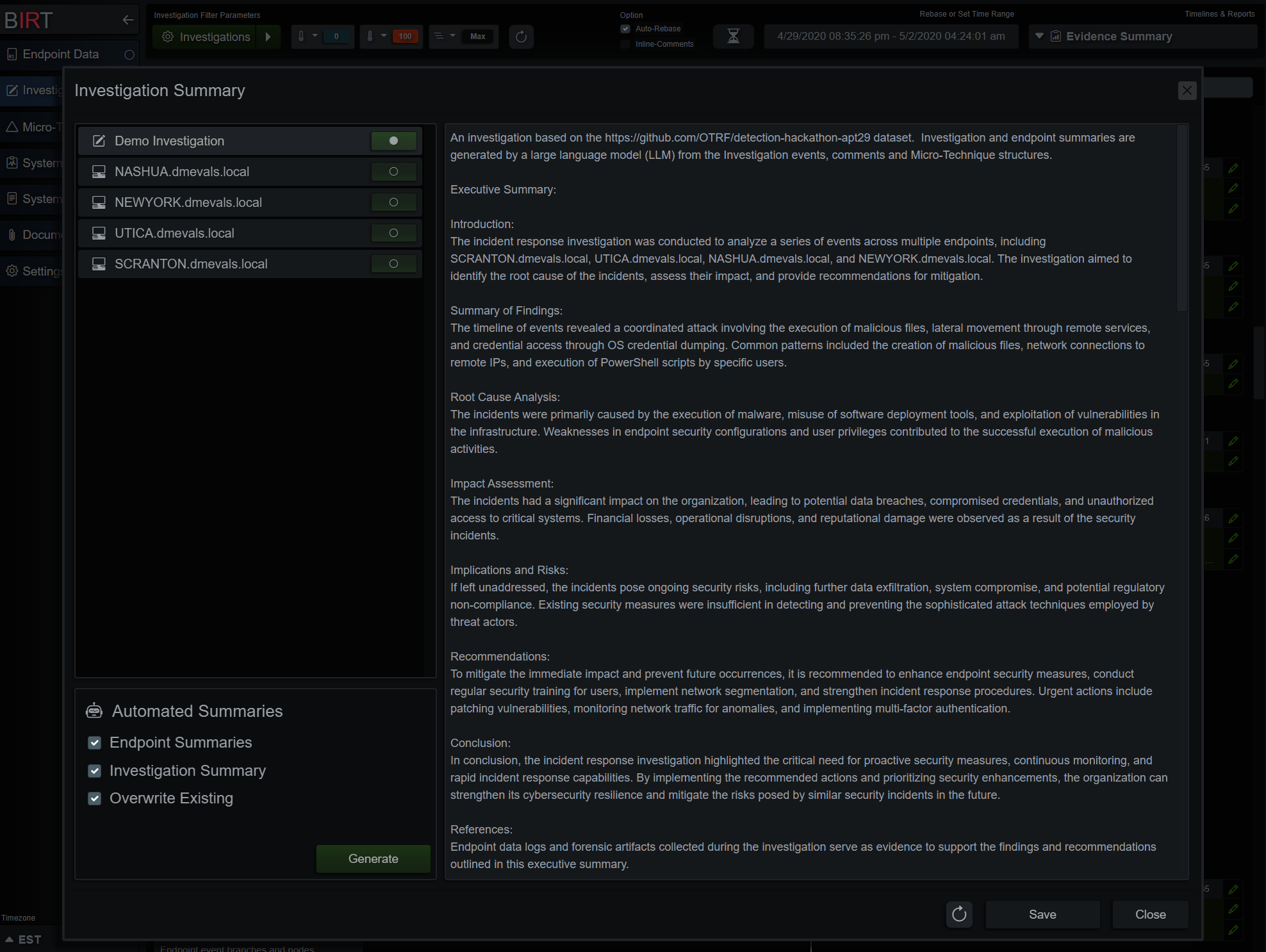
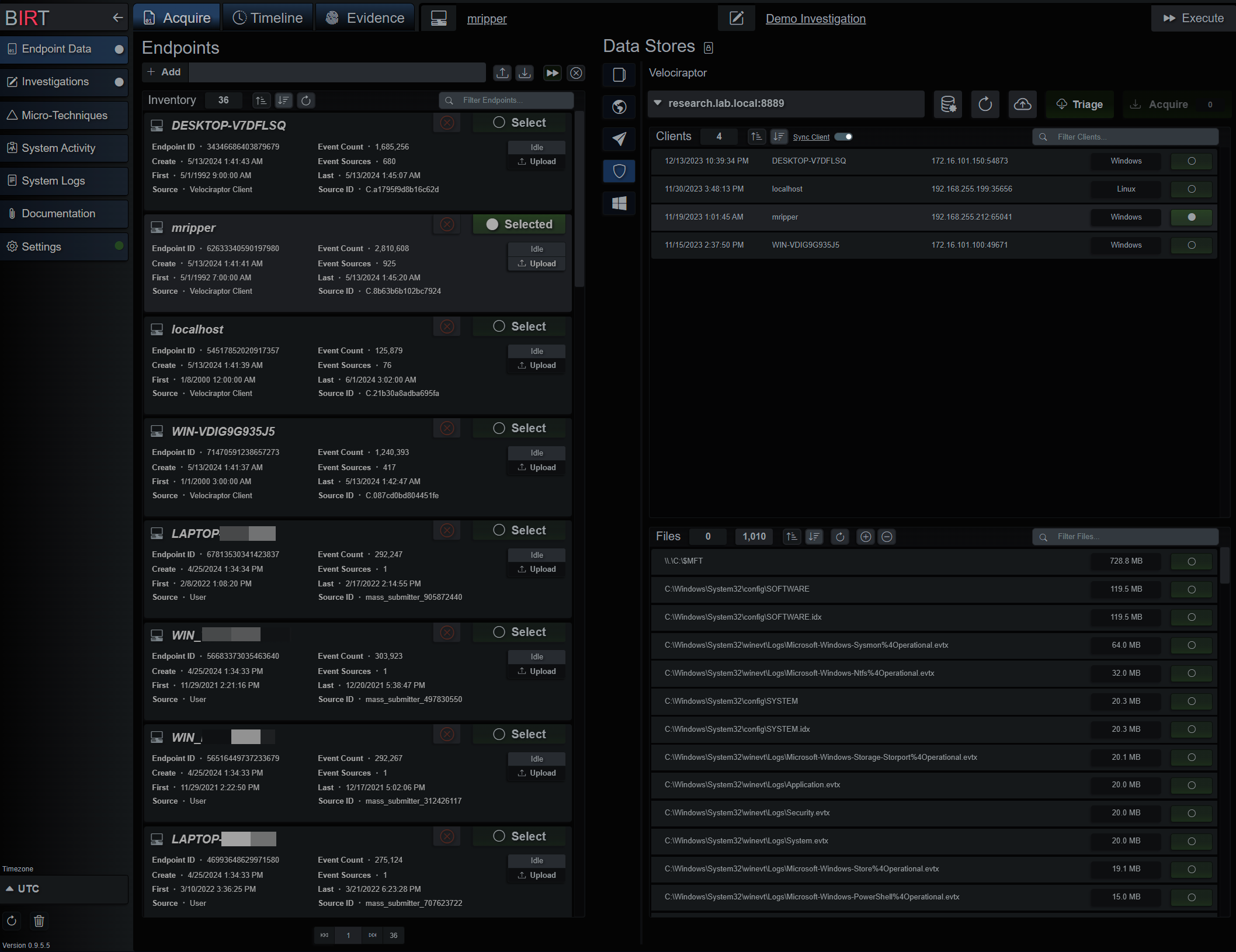
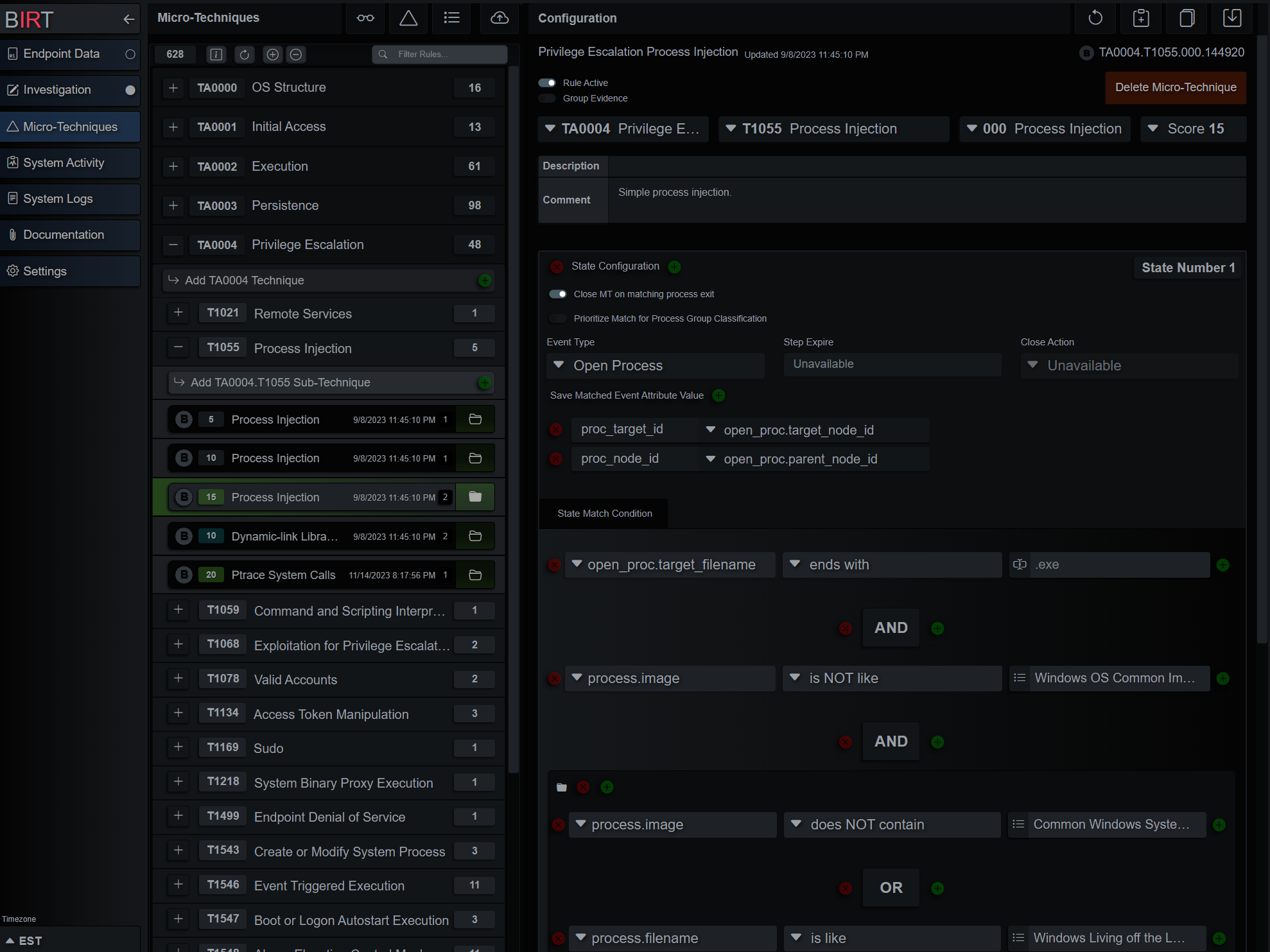
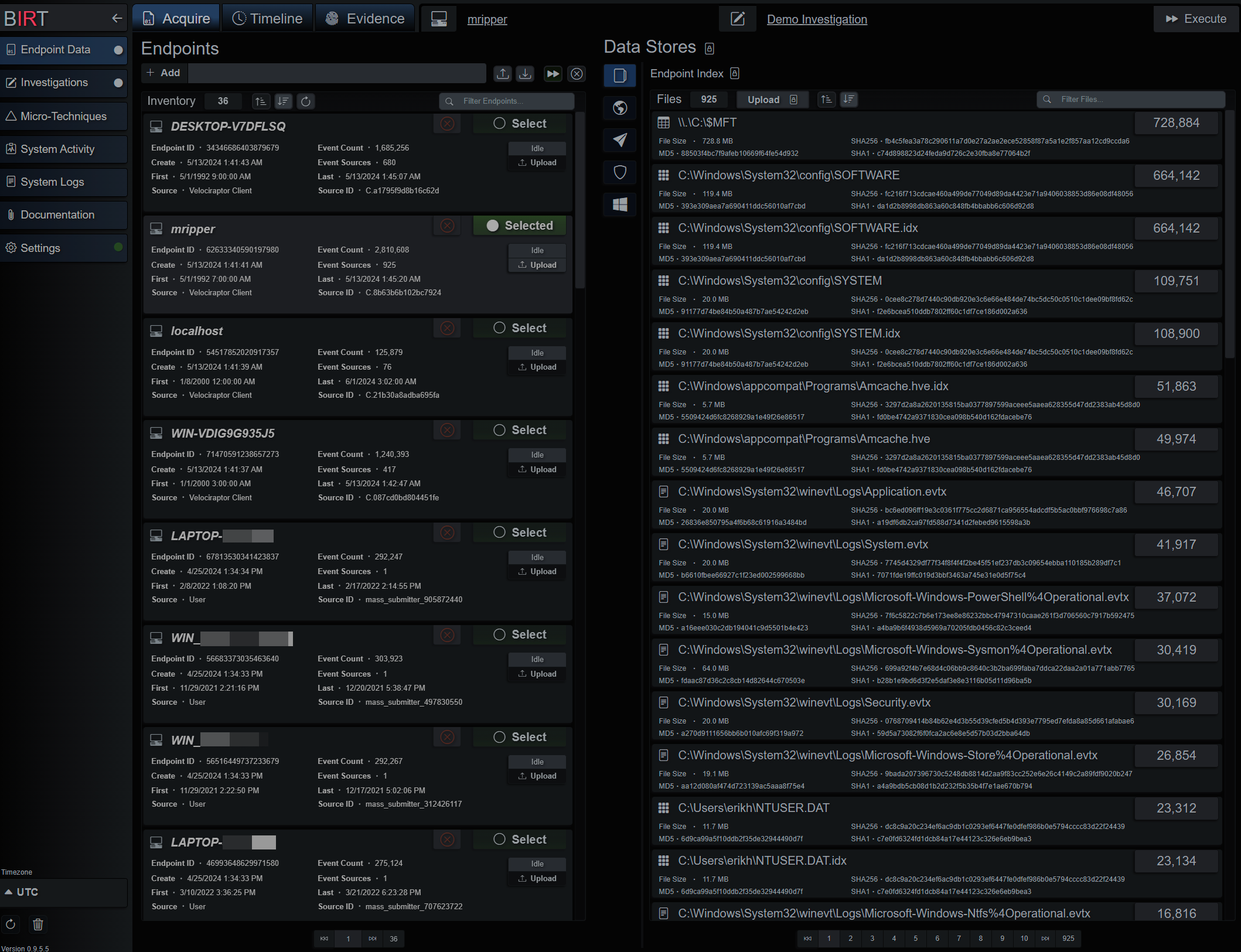
The Beta application will load a demo investigation based on data from the
detection-hackathon-apt29 Github repo.
That repo has been forked and the separated data can
be found
here. Unlocked evaluation licenses are available upon request.
Read the Docs!
docker pull thebirtproject/birt-beta:0.9.6.5
docker run -it -p 127.0.0.1:8080:8080 -p 127.0.0.1:8081:8081 thebirtproject/birt-beta:0.9.6.5
Browse to https://127.0.0.1:8080/ui/
Credentials; u: admin p: admin